Defense in Depth
Peplink technologies work together to generate a multi-layered defense against potential intrusions. To reach your network, attackers would need to defeat a battery of technologies, each defending a different part of the network from different forms of attack. Defenses are implemented on the client, router, SD-WAN, cloud, and administrative layers.

Client Layer
The client layer covers devices that end users interact directly with, as well as AP that delivers Wi-Fi to such devices.
Router Layer
These features can also be virtualized on the cloud layer. Having them both on the cloud and on the router makes it possible to secure local Internet breakout as well as VPN traffic.
Web Blocking
Each Peplink router has a dynamically updated web blocking tool that filters traffic into several categories. Users simply need to choose the categories they wish to block, and the router will take care of the rest.
Scalable Firewall and Outbound Policy
Outbound Policy and firewall rules are only effective if they are usable. With Peplink gear, you can set firewall rules based on application, and even by country. With InControl, you can also centralize firewall rules and outbound policy for multiple devices.
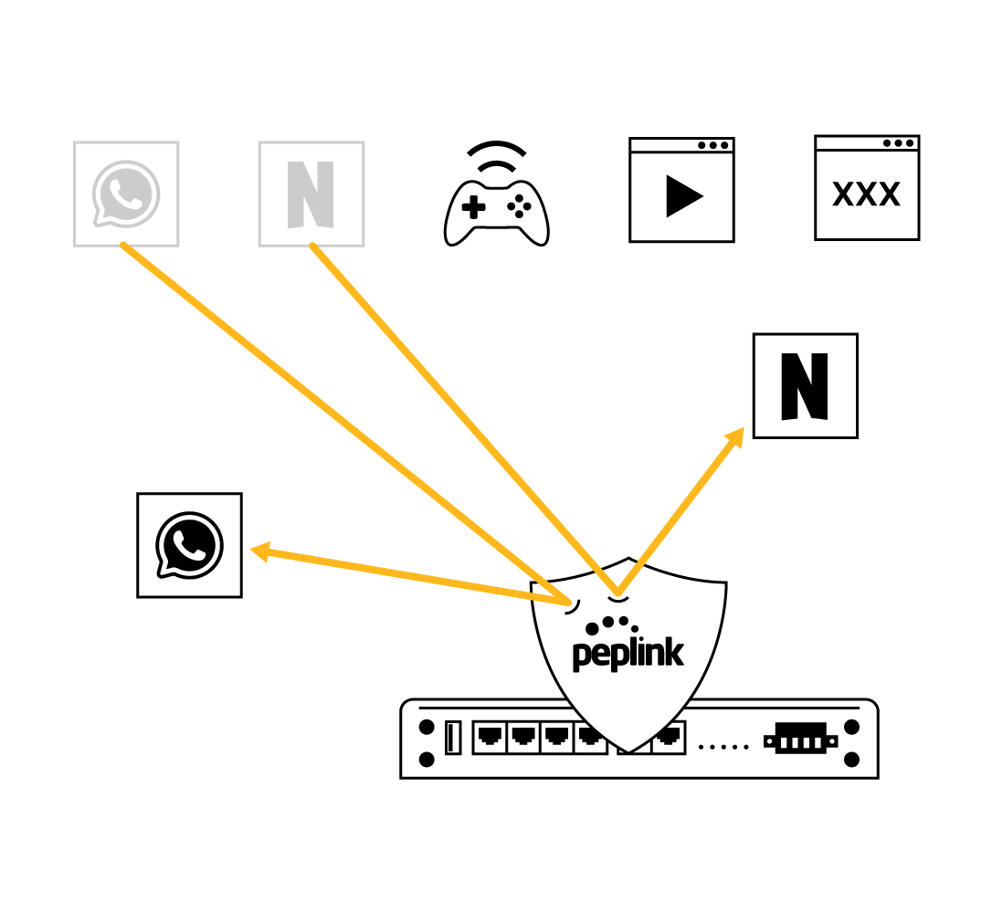
DPI Application Filtering
For applications that cannot be recognized by First Packet Inspection, there is Deep Packet Inspection. Block popular distractions such as streaming sites, social media platforms, and instant messengers.
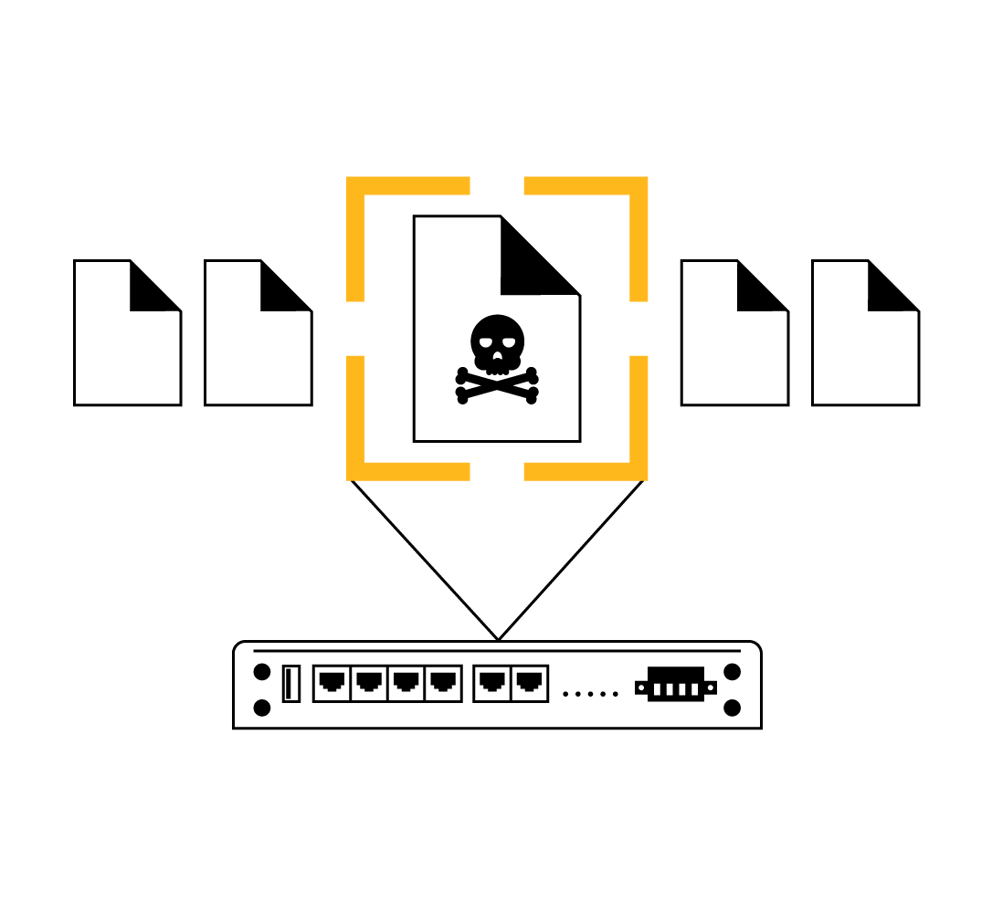
Intrusion Detection and DoS protection
Each Peplink router has a built-in DoS protection feature. Once enabled, it can detect and block abnormal packets as well as suspicious traffic typical of intrusion and denial of service attacks.
Security Patches
There are always new threats and vulnerabilities to be discovered. When one emerges, Peplink will quickly develop and deploy new firmware to address the threats. We update firmware for our products years after they have been launched. See Threat Response >
SD-WAN Layer
The SD-WAN layer covers the security of the data as it travels across WAN links. Peplink’s patented SpeedFusion technology provides a significant advantage on this layer.
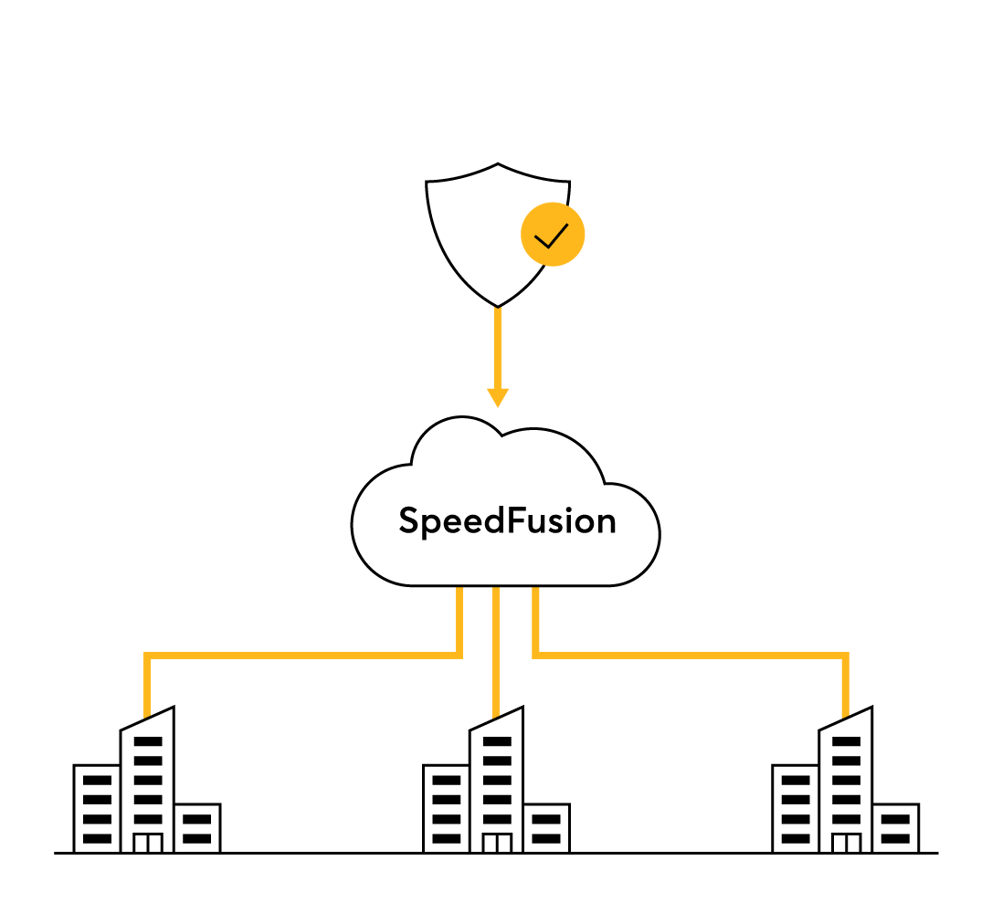
Cloud Layer – FusionHub
FusionHub can be installed on cloud services for cloud-based security. Combined with a Peplink router, and you can secure both organizational VPN traffic as well as branch office Internet breakout.
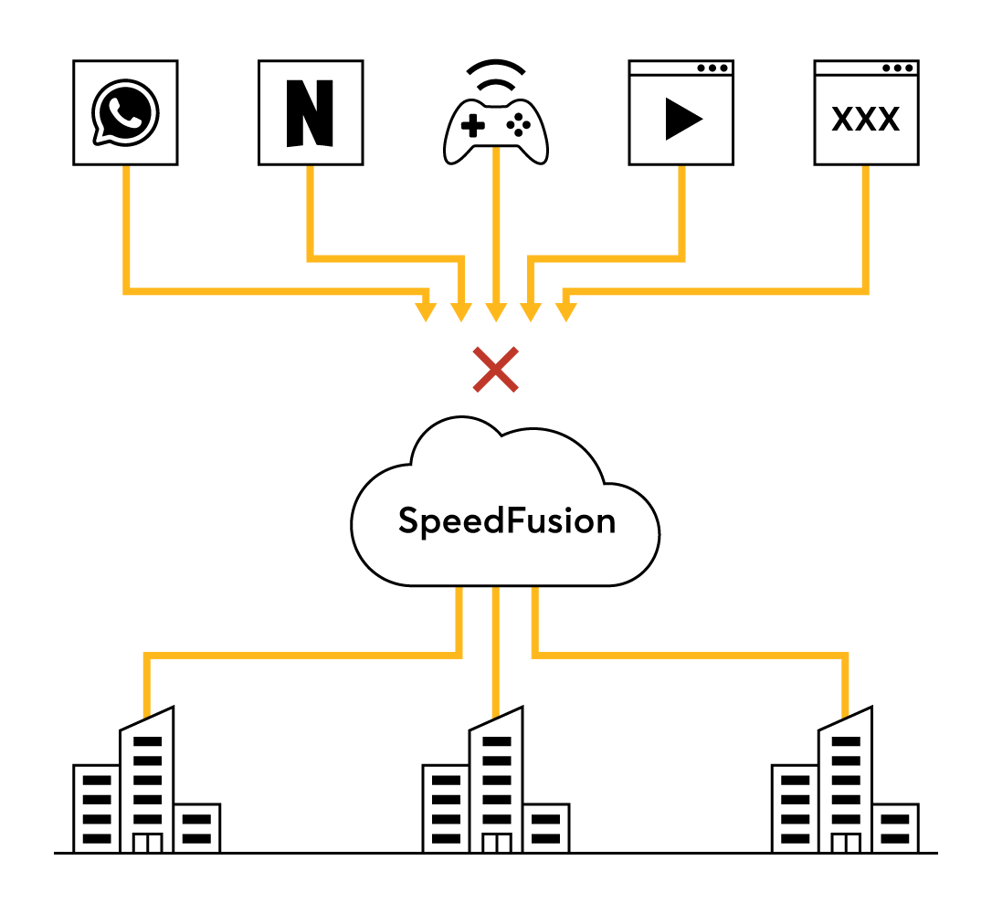
Comprehensive Traffic Security
Use web blocking, firewall, outbound policy, DPI application filtering to control what type of traffic can access your network. Protect your entire network with Intrusion detection and DOS protection. Any security feature that our routers have can also be applied to the cloud.
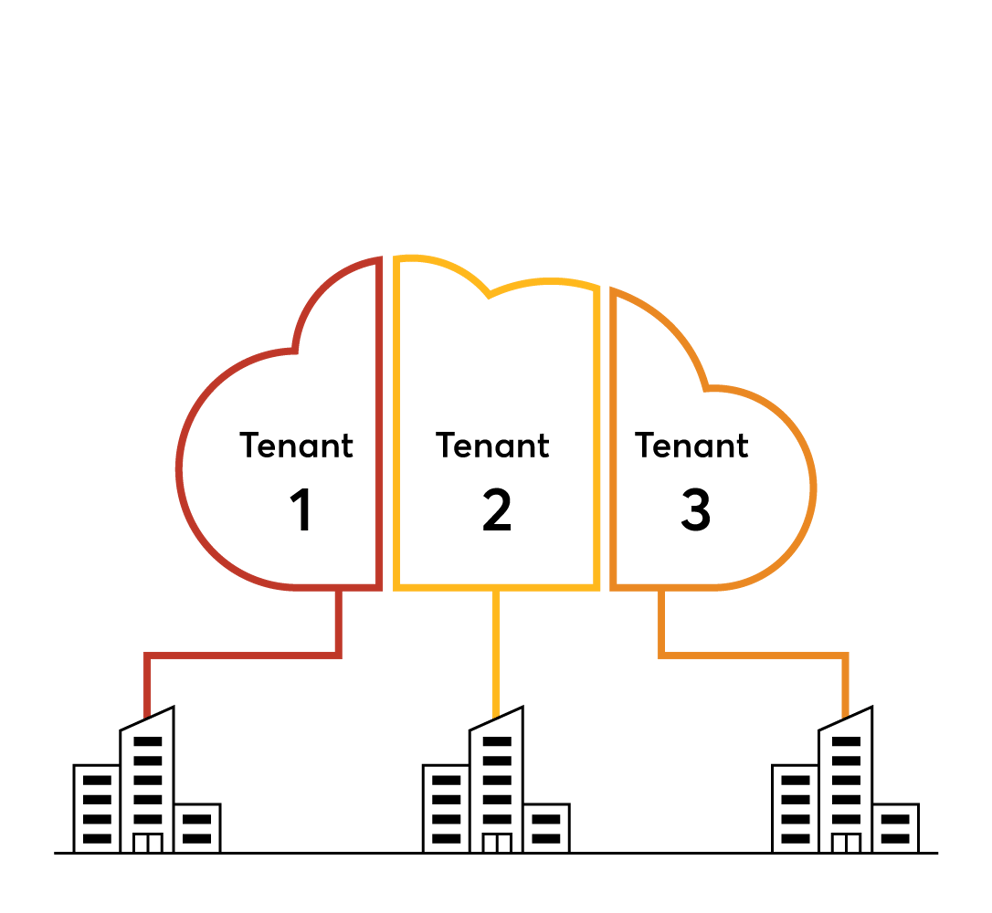
Tenant Segmentation
Our cloud appliance supports VRF, which divides the appliance into groups and holds a separate routing table for each group. The result: one cloud appliance can host several tenants, with each of them completely isolated from each other.
Security Patches
When vulnerabilities appear, we swiftly develop patches and make them available to our users. These patches are available on our cloud services as well as our routers, securing your entire network. See Threat Response >
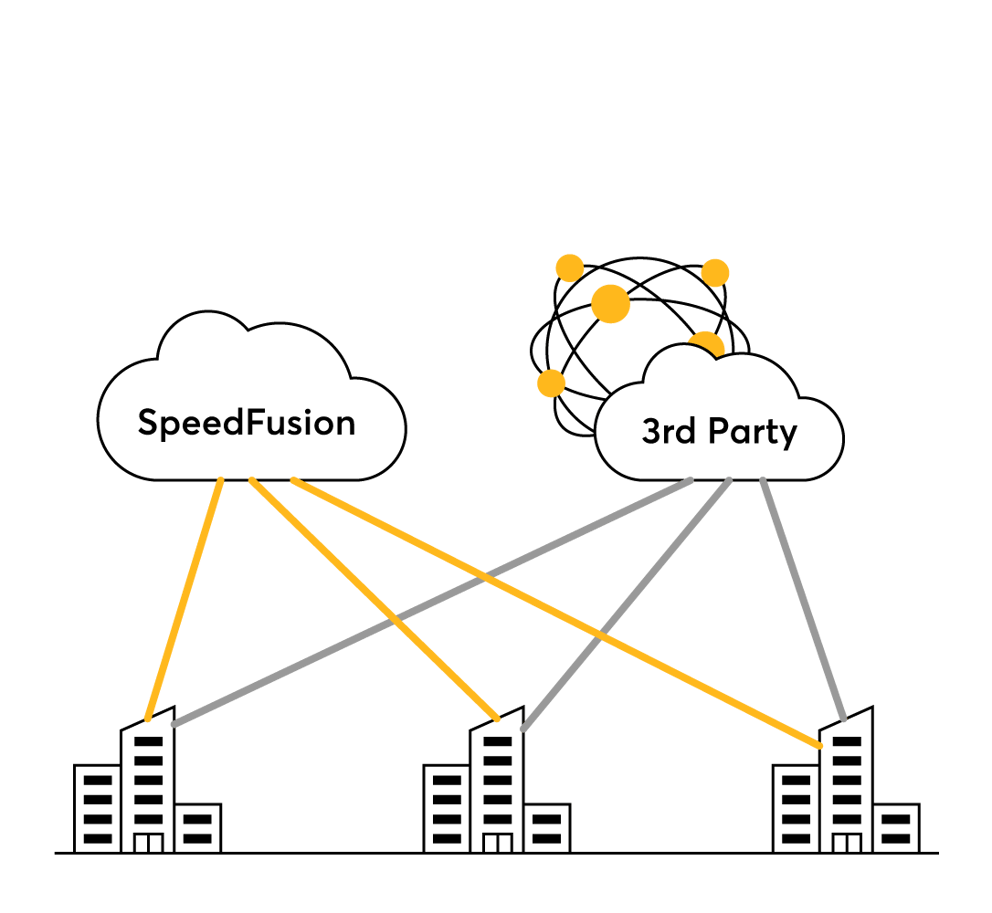
3rd-Party Security Integration
Works together with your 3rd-party cloud-based security solution. Secure organization traffic with our security features, and secure public Internet traffic with the 3rd-party solution of your choice using IPsec or OpenVPN. See Walkthrough>
Administrative Layer
The human layer covers credentials carried by an organization’s team members. Countermeasures protect passwords and minimize the potential harm done by a breach.
Easy Reporting Mechanism
Reporting a bug is really simple: simply open a ticket, enter your details, and a Peplink engineer will get back to you within 24 hours. We also have a vibrant community forum regularly patrolled by our engineers and partners. Ask your question there to stimulate discussion and possibly development.
Standards Compliance
Peplink also has equipment and features that can fulfill the security requirements of important compliance bodies.
PCI DSS V3.2 Compliance For Secure Retailing
Companies who are dealing with credit card and payment information must meet the requirements set by the Payment Card Industry Data Security Standards (PCI DSS). Peplink routers are capable of meeting PCI DSS 3.2 requirements. Learn More >
FIPS: North American Public Safety
Published by the U.S. National Institute of Standards and Technologies (NIST), the Federal Information Processing Standard (FIPS) is used by the U.S. government to approve cryptographic modules for encrypting network traffic. Peplink has a range of FIPS compliant products. Learn More >
Comprehensive Protection
Use Peplink technology to build a resilient network that is protected from threats on multiple levels. Use SpeedFusion bandwidth bonding to implement bulletproof packet-level security. Use InControl centralized management to centralize security policy and make network security scalable and easy to manage. Contact one of our skilled Partners to get started.